Around the globe, businesses and individuals had to do their best to cope with the COVID-19 pandemic. With everyday lives and normal business practices put under pressure due to virus-prevention measures, many employees were required to work remotely, and continue to do so in some capacity today. Unfortunately cybercrime has increased, as widespread remote work introduces new vulnerabilities cyber criminals can exploit, such as inadequate security measures, unsecured home network and human error.
According to the Insurance Bureau of Canada (IBC)*, “In 2021, 41% of small businesses that ever suffered a cyber attack reported that it cost them at least $100,000, up from 37% in 2019.” Canadian businesses, big and small, have all felt the impact of cybercrime.
Shared below are some key recommendations for businesses to help protect their operations against cybercrime while navigating a remote work environment. By implementing these recommendations, organizations can help to safeguard their business information and minimize their vulnerabilities to cybercrime.
Stay safe with 12 cyber security recommendations
Password complexity is essential
This is the first line of defense against cybercrime.
Strong passwords typically use capitals, lower-case letters, numbers, and special characters over a minimum number of digits. A minimum of eight digits is a good rule (the more the better), for example, $Magenta. The Canadian Centre for Cyber Security provides recommendations for best practices on their website. The National Cyber Security Centre in the UK recommends using three random words, for example, bluemonkeyflag. This password, in turn, is then made more complex and secure by adding numbers and special characters, e.g., 27bluemonkeyflag&.
Weak or easy-to-guess passwords are a common entry point for cyber criminals to gain unauthorized access to business information. For example, date, place of birth, favourite sports team, pet’s name, partner or child’s name should never be used.
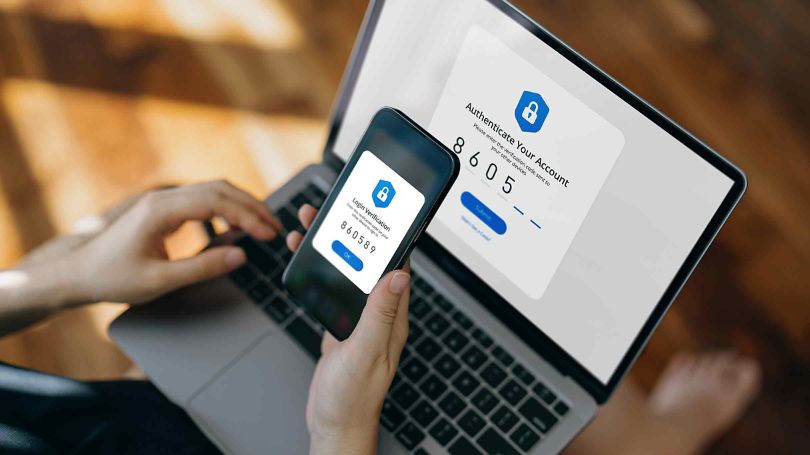
Utilize multi-factor authentication
Having two forms of identification is an additional layer of protection beyond just a password. This can be achieved by a password and then a randomly generated validation code, sent to a user by text message or an app.
Set user privileges across the organization
Individuals should only be granted access to those business systems, functions, software, and areas necessary for their job responsibilities. This helps prevent unauthorized access to business information and limits the potential damage that can be caused if or when a user account is compromised.
Employ Virtual Private Networks (VPN) for added security
Using a VPN adds an extra layer of security to online activities, as it extends a private network across a public network, allowing users to send and receive data as if their devices were connected to a private network. Private networks are designed to be secure and provide controlled access to authorized users, including password protection and encryption.
Restrict use of own equipment
Use of employee’s own equipment is not recommended for cybersecurity reasons as personal devices may not have the same level of security measures as business-owned equipment. A user's own laptop for example, may lack encryption, antivirus software and regular security updates. Personal devices for business purposes can also increase the risk for data loss and/or unauthorized access from sharing device with household members and may not be detected due to lack of monitoring.
Complete anti-virus and software updates as soon as they are available
Software updates can be a time-consuming irritation to users, but it cannot be emphasized enough that as soon as an update is available it should be completed. Each update will also include the latest security improvements.
Produce quick reference guides
Uncertainty about how to access the private network remotely, or unfamiliarity with different systems and applications, can increase query traffic to an IT Helpdesk. Production of easy-to-use 'How To' user guides can reduce pressure placed on the IT support team and reduce the chance of employees creating a security issue.
Train employees on common phishing tactics
Phishing is defined as untargeted, mass emails sent to many people asking for sensitive information such as login credentials or bank details. These emails can encourage individuals to click on a link or visit a fake website that can affect a user’s device with malware, allowing cyber criminals to gain unauthorized access to their accounts.
Institute removable media policies
SD cards, USB memory sticks and other removable media devices can introduce viruses into a computer, which can spread through a network. There should be a workplace policy that no removable media is to be used, and the ports on devices disabled to protect against this threat. Email or cloud storage should be used to transfer data instead.
Avoid the pitfalls of work in public places
There are three main things to keep in mind when using devices in public:
- Don’t leave devices unattended: Devices left unattended or unlocked are easy targets. Employees should always take the device with them.
- Be aware of surroundings: Can someone look over the user’s shoulder? What's on the screen and even the keystrokes could be compromised/captured.
- Avoid public wi-fi: A coffee shop wi-fi for example, with no password, provides easy access for cyber criminals. A mobile phone's 4G network’s built-in security and tethering is a superior option.
Use encryption for better security
This is the process of encoding a message or information in such a way that only authorized parties can access it. It will not stop a cyber incident, but it does make the data useless toa criminal if they were to maliciously access it.
Reporting Security Issues
Employees should be made aware that time is of the essence when it comes to reporting any security incident. Being able to assess the situation quickly and organize a suitable response could help maintain a level of security, limit losses, speed up recovery and increase the chances of a perpetrator being caught. The implementation of a cyber incident response plan can help prepare an organization for this type of scenario. To learn about the four steps to follow in an incident response plan, see Cyber Security: Respond quickly and recover faster.
In addition to the easy-to-implement cyber security recommendations above, the purchase of a cyber insurance policy is great way to protect against a wide variety of cyber risks. Cyber coverage helps proactively manage business risks and gives access to around the clock support from technical experts who can assist with cyber incident resolution. Cyber coverage will also help a business meet the requirements to comply with Canada’s Personal Information Protection and Electronic Documents Act (PIPEDA).
Navigating a remote work environment while protecting operations against cybercrime isn’t easy. However, applying these recommendations will go a long way to help safeguard business information and minimize vulnerabilities to cybercrime.
*Source IBC: www.ibc.ca/news-insights/news/many-small-businesses-vulnerable-to-cyber-attacks